Sen. Markey wants details on cyber threats to the U.S. grid
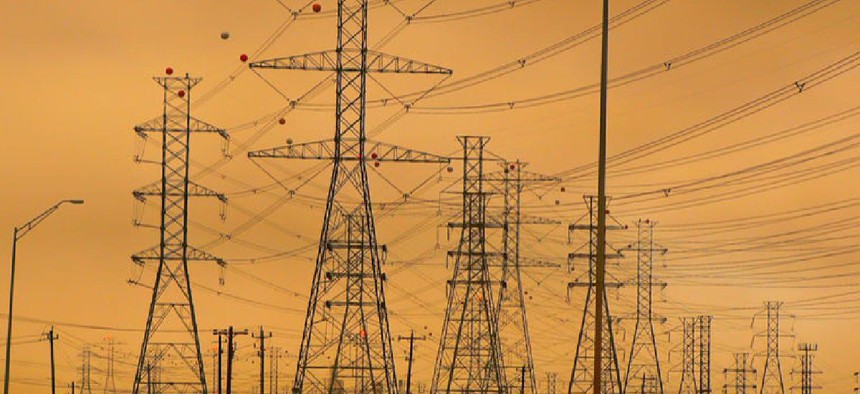
In letters to federal agencies and power companies, Sen. Edward Markey wants more information on reports of cybersecurity vulnerabilities in U.S. power systems.

A top member of the Senate Foreign Relation Committee's cybersecurity subcommittee wants briefings from information from energy companies and federal agencies on a reported breach of a power company's control system.
Sen. Edward Markey (D-Mass.), ranking member of the Foreign Relations Subcommittee on East Asia, the Pacific, and International Cybersecurity Policy, on Aug. 13 sent letters to federal agencies and energy grid and power utilities asking about the details of a Russian-backed cyber program aimed at breaching the control systems of U.S. electrical grid suppliers.
Markey wants answers by Sept. 7 from the Department of Homeland Security, Department of Energy, Federal Energy Regulatory Commission, 10 commercial power companies and federal power marketing organizations such as the Tennessee Valley Authority about their current efforts to prevent such intrusions.
DHS detailed some of the techniques the attackers used in 2017 breaches of industrial control gear at the utilities in a public briefing this July. Press reports suggested the attackers could have taken direct action to turn off the power system through the compromised controls.
DHS officials said during those public teleconferences that Russian hackers had claimed "hundreds of victims" in a sustained campaign last summer aimed at infiltrating industrial control systems of U.S. critical infrastructure providers. The officials said that the campaign could have resulted in ICS equipment being manipulated into disrupting electrical power flows.
DHS later clarified that intruder access to the industrial control system would not have had any impact on the grid. Experts on industrial control system cybersecurity also said the details of the DHS briefing, taken from previously reported incidents, showed that the danger of hackers bringing down the power grid wasn't imminent.
In an Aug. 6 blog post, industrial system threat detection provider Dragos said the Russian-backed intrusions described by DHS have not inserted "cyber implants" into the electric grid to cause blackouts. The company said the Russian intruders were infiltrating business networks, "and in some cases, ICS networks, in efforts to steal information and intelligence that could potentially let them into operational systems."
Markey is looking for details on whether utilities have been targeted by cyberattacks over the last five years and what steps had been taken to prevent future attacks, as well as other questions about preventative measures.
From the federal agencies, Markey wants information about how they are coordinating cyber defense activities; their efforts to engage third-party ICS vendors; and how they're increasing resiliency.
In mid-July, FERC set a final rule tightening cyber incident reporting for electrical providers, mandating they report cyber-intrusions that bump up against their perimeter cyber defenses or associated Electronic Access Control or Monitoring Systems, but don't actually get into providers' primary systems.
NEXT STORY: TSA expands scanning tech


