Cyber rules of engagement still unfinished
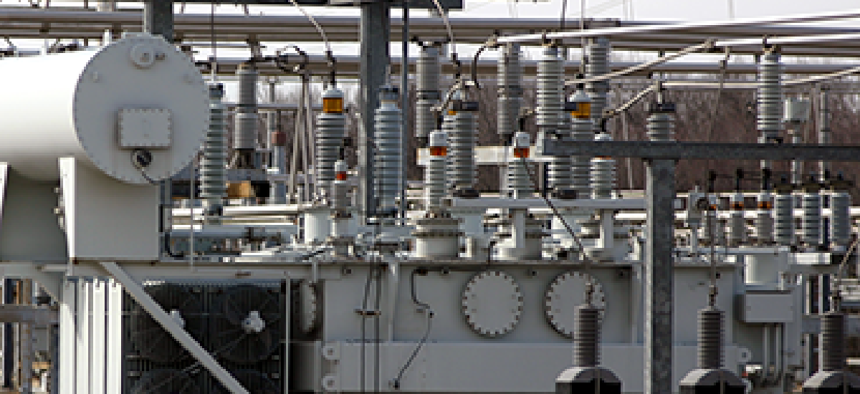
With the risk of a cyberattack against the nation's power grid and other critical infrastructure growing, the military's promised rules of engagement have yet to materialize.

A successful cyber attack could damage the nation's power grid and other critical infrastructure, but the rules of engagement needed to shape a military response are incomplete.
For months, Defense Department officials have been at work establishing the rules of engagement that will govern military action in cyberspace. Despite recent assurances of their imminence, those rules have yet to be finalized, and some say their absence could affect national security.
Defense Secretary Leon Panetta said in October that Pentagon leaders are close to finishing the rules of engagement, an official doctrine that will likely echo in structure the guidelines that regulate armed conflict. But will that be enough to address, on a national level, the constantly evolving landscape in cyberspace?
“The DOD rules of engagement are important, but there’s an issue of whether or not that’s suitable for era we’re in,” said Tim Sample, vice president and sector manager for special programs at Battelle, If the rules are modeled after the traditional rules and assumptions for conventional combat, that would be based on a 'faulty assumption," he said. “It can be argued whether that’s practical [to have] a traditional response to attacks in an era or environment that is by definition very untraditional."
Sample co-edited a book from Battelle on national cyber policy that is due out soon, called “#CyberDoc: No Borders, No Boundaries.”
According to Panetta, the cyber rules of engagement will make the U.S. military more agile and quicker to respond to cyber threats.
“For the past year, [DOD] has been working very closely with other agencies to understand where are the lines of responsibility when it comes to cyber defense. Where do we draw those lines? And how do those responsibilities get executed?” he said at New York event. “As part of that effort, the department is now finalizing the most comprehensive change to our rules of engagement in cyberspace in seven years. The new rules will make clear that the department has a responsibility, not only to defend DOD’s networks, but also to be prepared to defend the nation and our national interests against an attack in or through cyberspace.”
One challenge for establishing rules of engagement is that much of the critical infrastructure under threat -- the nation's power grid, financial networks and other essential systems -- are privately owned. Panetta has said repeatedly that collaboration with the private sector is crucial to create a policy that will protect the infrastructure.
At the Association of the United States Army conference in Washington last month, Lt. Gen. Don Campbell, commanding general of the Army’s III Corps and Fort Hood, Texas, echoed the need for military rules for cyber operations.
“How far can we go to target this network or that network or capability or system? We’re going to have to decide as a service or military,” Campbell said.
According to Sample, the U.S. needs a broader strategy for national security in cyberspace that encompasses more than only the military. Today’s national security policies are rooted in the Cold War era – a bygone era outdated by the vulnerabilities of reliance on technology.
“The national-level doctrine that we had – defined as a priority in direction that guides government and industry and even individual citizens – really was doctrine of containment after World War II. After the Cold War, containment fell by wayside and never really was replaced,” Sample said. “Now, the stakes are higher. We are much more vulnerable because of our reliance on the Internet and technology. We’ve created a myriad of positions, policies and legislation to evaluate vulnerabilities as they emerge. The problem is that it’s basically unconnected; it’s lacking in the overall focus that we’d have in a national doctrine.”
While DOD’s rules of engagement will direct military action in cyberspace, a wider national-level doctrine should lay the groundwork for a more comprehensive range of issues related to cybersecurity, from federal guidelines to everyday activities, Sample said.
For example, in the Cold War era there was an understanding of responsibility at the individual citizen level – take, for example, the drills in which schoolchildren would take shelter under their desks in preparation for a nuclear bomb. While that activity itself is an obsolete idea now, it represents the reach a national doctrine should have, Sample noted.
“The difference [from the military ROE] is that the doctrine, in essence, is an overarching structure or framework that everything else should be fitting into. It’s not just DOD, Homeland Security or the intelligence community; it really is laying out a path and direction for where we want America to move in this cyber era,” he said. “We need to start out by laying down overriding principles…not just in cyber but where the country goes and what our long-term objectives are. We have to have a doctrine that is adaptable and agile. Having an override principle and doctrine will help guide us in a way more effective than what we’re doing today.”
NEXT STORY: 10 tips to keep data secure


