The root causes of government IT insecurity
In the first of three columns, a former government executive discusses what's really needed to prevent another massive data breach.

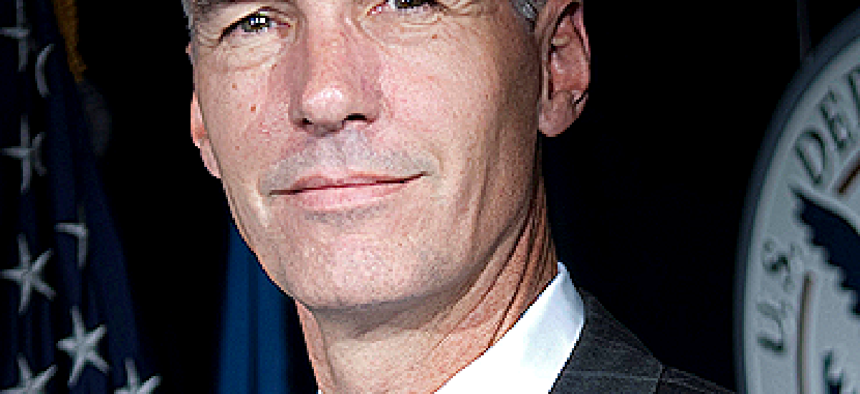
Richard A. Spires sees lack of best practices, misguided security and cumbersome acquisition at the heart of the federal IT security problem.
In June, I testified before the Senate Appropriations Committee’s Financial Services and General Government Subcommittee about the recent Office of Personnel Management data breaches. Given that I never worked at OPM, my testimony described broader systemic issues that must be addressed if we are to better protect our government’s data and IT systems.
I am presenting the substance of that testimony in a series of three columns covering the root causes of the government’s IT security issues and offering recommendations to address them.
Three primary root causes have led to the massive data breaches and compromises of core mission IT systems at multiple federal government agencies.
1. Lack of IT management best practices. The very best cybersecurity defense is the result of managing IT infrastructure and software applications well. During the 1970s and 1980s, agencies could build and deploy IT systems with little regard to security issues. That was not necessarily a management failure because there were few security issues to be concerned with prior to the broad use of the Internet and the rise of ubiquitous data networks.
Beginning in the 1990s and up through the present, however, the federal government has not properly managed its IT because it has failed to effectively adapt with the changes in IT and the evolving cybersecurity threat.
For example, when I served at the IRS and then at the Department of Homeland Security, we would all too routinely discover IT systems outside the IT organization’s purview that had been developed and deployed without the proper IT security testing and accreditation. That highly distributed approach to IT management has led to the deployment of thousands of data centers across the federal government.
Today federal agencies struggle to manage and maintain that dispersed infrastructure and those disparate systems. In far too many instances, hardware and software assets are not systematically tracked, software is not routinely updated and patched, and critical hardware and software have reached their end of life and, in some cases, are no longer even supported by the vendors.
And although I am a big proponent of cloud technology, I am concerned that many agencies are not necessarily using cloud capabilities to streamline and simplify their infrastructures but instead are creating new stovepiped IT infrastructures. The complexity of maintaining a sea of vastly different systems in an ocean of differing IT infrastructures makes it impossible to properly secure an agency’s IT environment.
The federal government has not properly managed its IT because it has failed to effectively adapt with the changes in IT and the evolving cybersecurity threat.
2. Misguided IT security practices. Although well intentioned and appropriate for its time, the Federal Information Security Management Act (FISMA) skewed the government’s approach to securing IT information. Passed in 2002, the law set a course for how IT security effectiveness has been measured in government.
Although the law has some good components, the unintended consequence is that it forced chief information security officers to focus on the controls for individual systems. In reality, IT systems across the government were already becoming more interconnected, and viewing systems in isolation hid the impact on the larger enterprise security posture.
Further, based on guidance from the Office of Management and Budget, FISMA was implemented at a time when cyberthreats were still emerging and technology had not yet evolved enough to necessitate a security development life cycle.
In fact, until very recently, systems were certified and accredited on a three-year cycle. That cycle might be manageable, but it is comical when looking at the rapid evolution of technology and the cyberthreat environment. Furthermore, FISMA required the generation of paper-based reports that diverted time, resources and personnel from effective security efforts.
At the IRS and then DHS, I was consistently reluctant to put my confidence in the yearly FISMA reports because they did not reflect the reality of our overall IT environment’s security posture. That can only be accomplished through the proper use of tools that continuously monitor the IT environment and react to and mitigate threats in near-real time.
3. A slow and cumbersome acquisition process. The problem is exacerbated when funds are available to invest in IT security yet it is ponderously slow and difficult to buy commercial solutions to help address vulnerabilities. When I was at DHS, I was a proponent of the Continuous Diagnostics and Mitigation program but was dismayed to see how long it took (two-plus years) just to implement Phase 1. And then agencies had to go through an additional competitive process within the CDM program to obtain capabilities.
I am all for fair competition, but with sophisticated adversaries that will exploit any and all vulnerabilities, the government amplifies its vulnerabilities when it takes many months (if not years) to procure and deploy new IT security capabilities.
Those root causes have led us to the current situation of the government paying a huge economic cost because of inefficiency, duplication and unsecure IT systems and infrastructure. And what is worse, we will now likely pay an even greater cost in the exposure of the personally identifiable information of millions of current and former government employees — certainly in terms of those individuals’ privacy and potentially in terms of our national security as well.
My next two columns will cover recommendations for addressing those root causes, including the importance of properly implementing the Federal IT Acquisition Reform Act and the update to FISMA.


