DHS tags election systems as critical
Some state government officials object to the Department of Homeland Security's move to add election infrastructure to the roster of 16 existing federal "critical infrastructure" areas.
To the consternation of some state government officials, the Department of Homeland Security on Jan. 6 moved to make state election systems part of the critical infrastructure sectors under its protection.
The move comes in the wake of allegations of Russian hacking into political targets during the recent election period, and specific complaints of attempts to penetrate state election and voter data systems.
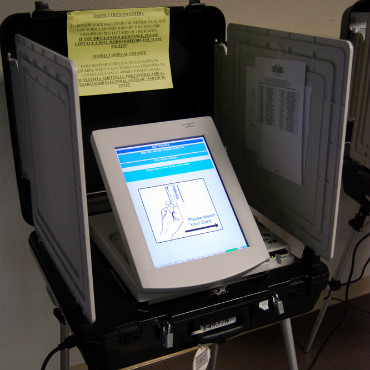
On Jan. 6, DHS Secretary Jeh Johnson formally designated state election assets -- including polling places; centralized vote tabulation locations used to support the election process; storage facilities; and related information and communications technology -- as U.S. critical infrastructure.
This includes voter registration databases, voting machines, and other systems that manage the election process and report and display results on behalf of state and local governments.
Johnson said that election infrastructure is now a subsector of the existing Government Facilities critical infrastructure sector.
Under the designation, Johnson said, state governments can ask DHS for help to secure their election infrastructure. And he stressed that such assistance was not mandatory.
"This designation enables the states, should they request it, to leverage the full scope of cybersecurity services we can make available to them," he said.
That didn't sway some state officials who had opposed the move, however.
"This provocative but predictable decision moves the federal government one step closer to controlling the elections process," said Georgia Secretary of State Brian Kemp in a Jan. 6 Facebook post after Johnson's announcement.
Kemp has been a vocal opponent of the designation since it was first suggested by DHS last summer. "I am completely opposed to this blatant overreach and will continue to fight to keep election systems under the control of state government where it belongs," his Jan. 6 Facebook post said.
Other state officials were concerned as well. "We take election cybersecurity seriously & welcome added attention to the issue – concerns about what 'critical infrastructure' means," said Vermont Secretary of State Jim Condos in a Jan. 7 tweet.
The National Association of Secretaries of State in a Jan. 9 statement called the new designation "legally and historically unprecedented and raised questions for states and local governments about administration of the voting process."
"While we recognize the need to share information on threats and risk mitigation in our elections at all levels of government, as we did throughout the 2016 cycle, it is unclear why a critical infrastructure classification is now necessary for this purpose," the group said.
Former U.S. CERT director Ann Barron-DiCamillo told FCW in a Jan. 9 email that the designation clears away a practical obstacle for states and local governments to ask for assistance from DHS. Prior to the designation, state election substructures, she said, weren't part of state government-designated infrastructure. That set-up made it difficult for DHS to offer assistance.
"As a whole, election officials have rendered virtually zero defense against the hyper-evolving nation state and mercenary adversaries that threaten our democratic process," said James Scott, senior fellow at the Institute for Critical Infrastructure Technology.
"At the state level, election officials have failed miserably to protect their networks, tabulators, voting machines, voter registration databases and polling places from outside cyber kinetic threats," he said.
Frank Cilluffo, director, Center for Cyber and Homeland Security, George Washington University, said the designation was "more of a bureaucratic enabler" that gives states voluntary access to faster help from DHS, not a power grab by the federal government to get control of the electoral process.
"It's good news that DHS has declared election systems as critical infrastructure -- anything we are doing to bring new resources and capabilities to bear on the threats to our elections is a good thing, and this declaration will help improve collaboration and quickly mobilize responses if attacks materialize in the future," said Nathaniel Gleicher, former director for cybersecurity policy at the White House National Security Council and now head of cybersecurity strategy at Illumio.
In announcing the designation, Johnson said he was sensitive to potential objections from the states. "Prior to reaching this determination, my staff and I consulted many state and local election officials; I am aware that many of them are opposed to this designation," he said.
He moved forward despite that, Johnson explained, because the designation makes election infrastructure a priority within DHS' National Infrastructure Protection Plan; enables his agency to prioritize cybersecurity assistance to state and local officials; and puts the same special government-backed seal on election systems that power, financial and other national critical systems have.
The designation itself, Gleicher and Cilluffo agreed, doesn't really make the election process more secure. It rather points to more work needs to be done by state governments and federal agencies to really protect election infrastructure.
Gleicher noted, for example, that the designation "does not cover political organizations or political operators – the primary targets of Russian operators during the last election."
"Much of cybersecurity today is still costly and complex, making it hard for short-term organizations like political campaigns to deploy it effectively," Gleicher said. "If we're going to secure our elections going forward, we need better tools for these security have-nots as well as the security haves."


